| Provisioning & Deployment pipelines for Backup, QA, staging & production working | Your Github Actions should all be running without any errors in logs. No red crosses! |
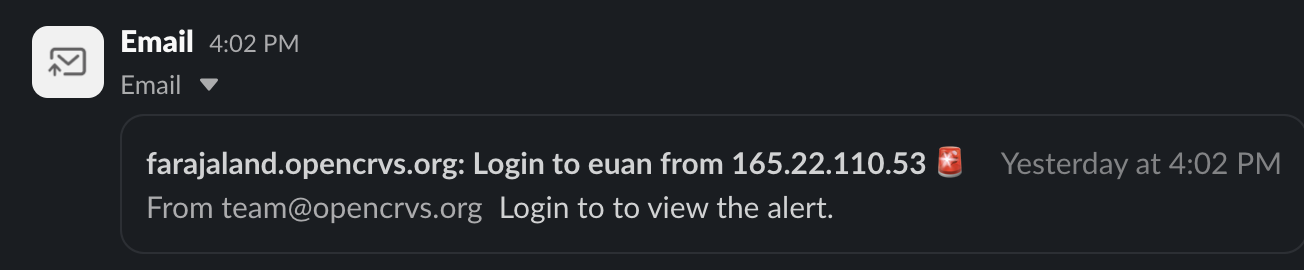
| SMTP service tested for emails and alerts | Not only should you confirm that emails are sending for staff, but you should receive emailed alerts too. If you have enabled Slack as the ALERT_EMAIL you would see an SSH login alert in Slack like this: 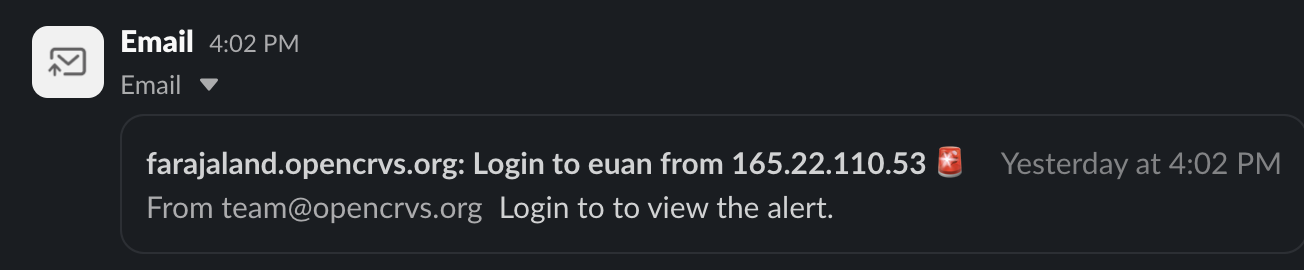 |
| Setup DNS & TLS (HTTPS) | Your SSL certificate should be valid.  |
| Verify production backups restore on staging (pre-prod/mirror) | Ensure that the backup & restore test is completed as documented. |
| Alert sent of SSH login | Ensure the SSH login alert is firing as mentioned above in the "SMTP service tested" description. |
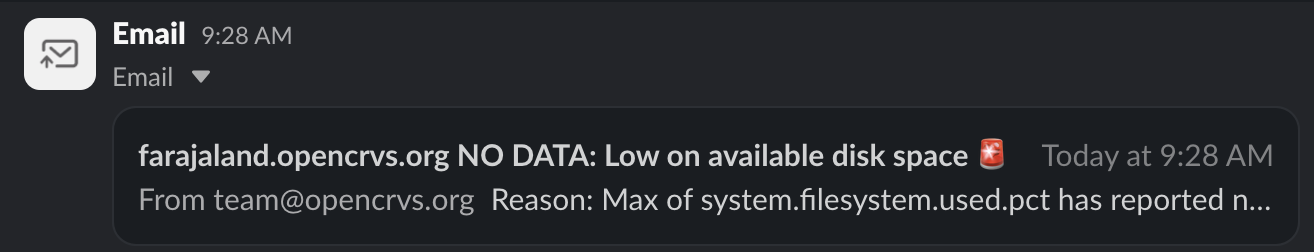
| Verify a warning is received when disk space is at 50%, alert at 70% | To test this you need to create a temporary large file on your server. Kibana will broadcast an alert. 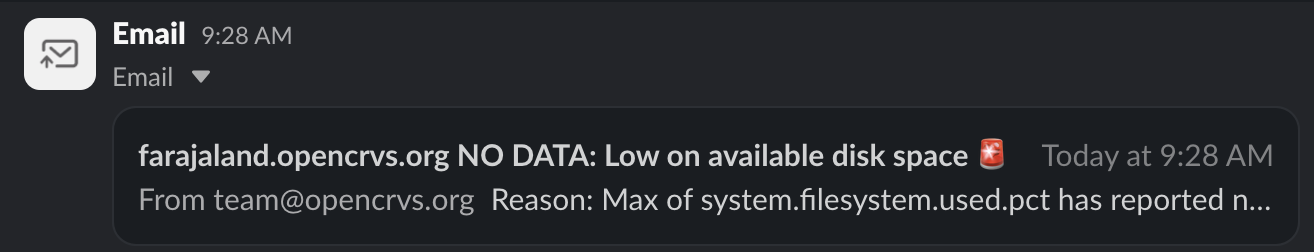 This example terminal command creates a file of 200G: This example terminal command creates a file of 200G: sudo dd if=/dev/zero of=/large-file-to-trigger-alerts bs=200G count=100.
|
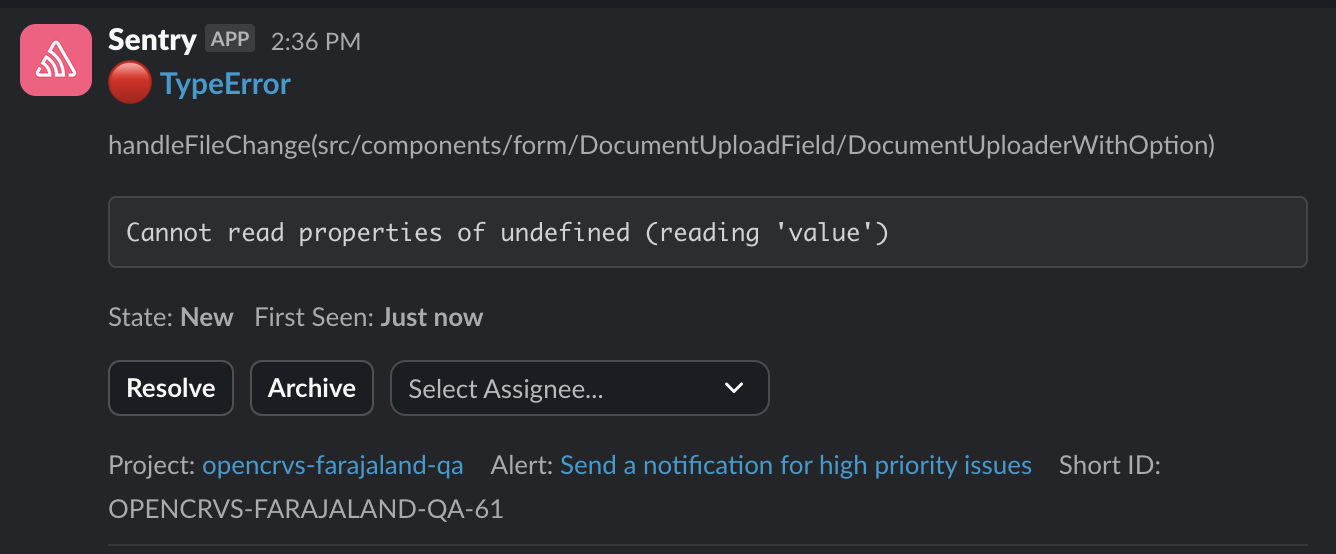
| Optional: Confirm Sentry errors to Slack from QA, Staging and Prod | A test Sentry error in Slack looks something like this: 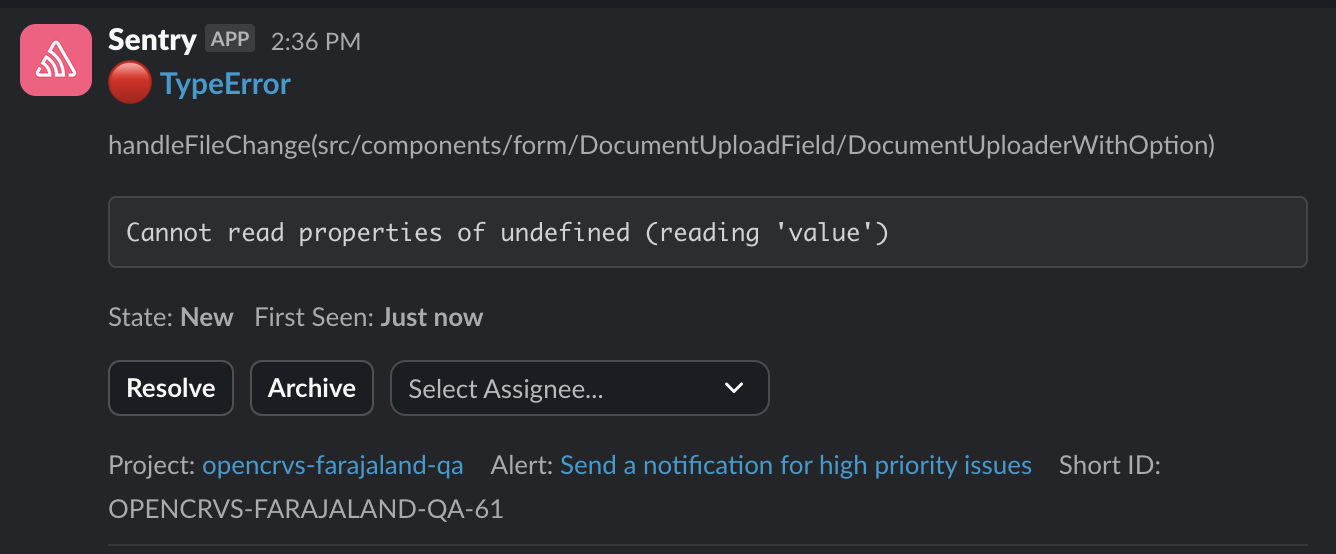 |
| Are National System Admin passwords updated, minimum 12 chars long and stored in a Password Manager. | The National System Admin must immediately change their password from the password that exists in prod-employees.csv . As they are a super user, they must confirm that the new password is saved in a password manager tool. |
| Github account is owned by country and OpenCRVS Core team are removed as admins | If the OpenCRVS team have assisted you to set up your Github organisation, they must no longer have "Admin" rights in your countryconfig repository otherwise they can potentially access citizen data. |
| Verify firewall hides all ports from the public internet | OpenCRVS should not be accessible on the public internet. But if you decide to do this at your own risk then this command can help you discover open ports: nmap --open opencrvs.domain.com |
| Clear all data from production instances created during testing | Reset the production environment so that it is clear of any test registrations. |
| Delete all test backups on backup server | SSH into the backup server and delete any test backups. Especially if you have configured the backup server to store more than the default 7 days of backups. |
| Delete all terminal history on all production, staging and backup servers | You might have exported secrets in Terminal to use when resetting environments or debugging. Clear the terminal history like this: history -c
history -w
|
| Remove OpenCRVS team members from SSH access to production, staging & backup servers | If the OpenCRVS team have assisted you to provision your production, staging and backup servers, their SSH access must be removed otherwise they can still access citizen data. Follow the steps as documented here. |
 This example terminal command creates a file of 200G:
This example terminal command creates a file of 200G: